ESP - Compliance Scope
Reduce compliance scope through micro-segmentation
The ability to meet IT security compliance requirements provides your company with many critical business advantages. But those advantages also come with the increased operational costs and complexity. Not being able to continuously maintain and demonstrate proper levels of compliance increases the risk of liability in case of a breach. But can these compliance goals be met while keeping the costs and liability risks at the absolute minimum?
Yes you can, and one of the best way to achieve that is "scope reduction".
Compliance Scope is defined by those parts of your IT environment that must meet the control objectives outlined in the compliance standards your organization is required or has decided to implement. If your network does not have clear and strong boundaries separating various network environments, your entire network may be in-scope, and therefore must meet all control objectives, including (potentially) ancillary requirements such as application security testing, penetration testing, etc. This is not desirable, but it can be remedied.
Managing compliance scope with Elemental
The Elemental Security Platform's (ESP) unique and versatile dynamic grouping capability combined with its adaptive micro-segmentation features are key to addressing the problem of limiting compliance controls to a predetermined and reduced logical zone of your network. This helps optimize cost, reduce time of audits and avoids unnecessary burden on the rest of the network. ESP’s micro-segmentation allows for creating logical boundaries between endpoint systems holding specific data that is subject to governmental or industry-mandated regulations and all other systems on the network. ESP makes it easy to quickly define any type of logical boundaries necessary to define the compliance scope, furthermore ESP automatically and continuously maintains a specified set of security controls in place to be checked on and enforced. These controls are available and ready-to-be deployed with the click of a button directly from the ESP Policy Library which gathers hundreds of security policy templates that have already been defined and organized in policy templates after the most popular industry security standards and regulatory compliance frameworks.
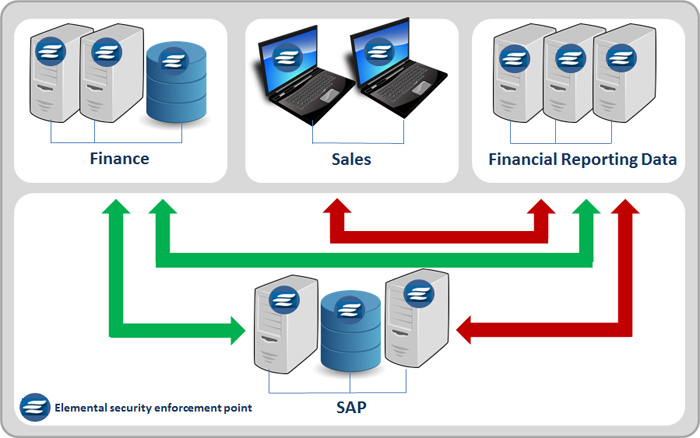
Security administrators determine and group any machines, no matter their location (on premise, cloud, datacenter, edge) or type (physical, virtual), that might contain documents subject to Sarbanes Oxley (SOX) requirements in a 'SOX security group'. Appropriate security controls are then deployed to all machines in the SOX security group. These actionable controls deployed through the Elemental Security Policies can optionally limit access between in-scope machines and any other host groups in the network. As a result, the SOX IT audit can now be limited to only the machines in the SOX security group.
Of course, the same strategy could be used for meeting any compliance scope reduction requirements driven by other mandates like: NIST, PCI, HIPAA, HITRUST, FISMA, etc.
Using ESP’s adaptive micro-segmentation, security professionals can not only lower the cost of the compliance assessment to fewer endpoints, but also deploy much more stringent security policies to the systems in high-security zones without having to subject out-of-scope machines to the same policies.